Security Group and ACL
Security Groups : what purpose ?
A security group contains one or more security rules :
- The rules are wether on incoming traffic, or outgoing.
- Allows to authorize TCP/UDP/ICMP data packets from or to a CIDR or another security group
- The default rule allows a machine to contact and be contacted by any other machine in the same Security Group, and allows any outgoing traffic.
VPC Peering
VPC Peering is a feature which creates a link between to VPCs in Flexible Engine
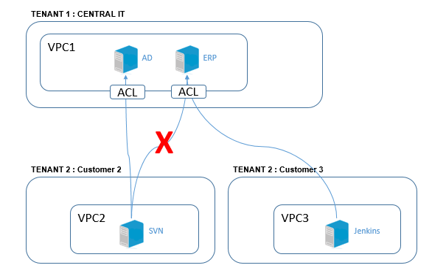
- Works between local (same tenant) VPCs as well as remote ones (different tenants)
- In both cases, the peering must be allowed and activated by both sides of the link
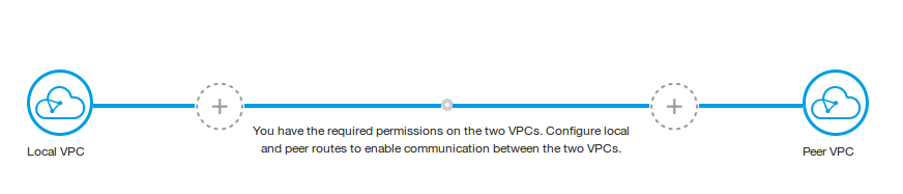
A VPC Peering is configured by setting routing rules specifying which CIDR can go through the peering.
Thoses rules must be on both sides of the peering, otherwise you might have networking issues
- A Multi-peering architecture can allows the centralization of multiple traffics.
ACLs in VPC networking
Network ACL (Access Control List) are an addition (and optionnal) layer of network security in a VPC which :
- Works like a firewall appliance contrôling network traffic going in or out of subnets
Network ACL use the same type of rules as Security Groups and can be used together.
- Creates a second security layer on top of Security Groups to globally restrict traffic
Access List come in help of security groups.
- Fro example, to block entire CIDRs or protocole on a wide range of machines without having to set each of them with a security group.
- To restrict which IP in a company can access certain services, in the case of IT Cloud infrastructure
The ACL rules are applied on whole subnets in a VPC.
In the case of traffic between Cloud instances, for example through VPC peering, ACL allows to manage more precisely what is authorized and what is forbidden to go in other VPCs.
ACL versus Security Groups
| Security Groups | Network ACL |
| Works at the server level (first level of protection) | Works at the network level (Second level of protection) |
| Applied automatically to an instance if the setting is activated, or afterwards when modifying the instance settings. | Applied automatically on all instances created on the affected subnets. ("safe" layer of security, as an instance can have wrong security groups.) |
| Rules are on source IP or destination IP | Rules can be on source IP and destination IP |
| Both are stateful : return traffic is allowed by default, unless explicitely forbidden. | |
| All rules are evaluated before making a decision on the packet | Rules are treated sequencially to determine is the traffic is allowed. |